In Part 1, we addressed some of the negative perceptions that exist for cyber insurance, the need for a standalone cyber policy and the difficulty carriers have in pricing premiums. In Part 2, we will explore the premium pricing practices and what to look for in a cyber policy.
How Do Carriers Price Premiums?
According to Founder Shield, underwriters use the following information to price cyber insurance premiums.
- Systems vulnerabilities
- Security training protocols
- Loss history
- Types of data collected and stored
An Advisen whitepaper from 2014 indicates that cyber policy underwriters are also interested in the amount of data a company retains, where data is stored (company server or cloud), and vendor management controls. But, there is no mention of loss history or security training.
In 2016, Jeremiah Grossman, Chief of Security Strategy at SentinelOne said to ITSPmagazine that premiums were based on only two factors – the company’s industry and the number of records it’s stored. In 2017, he added revenue to the equation in an article with Insurance Business.
What’s more interesting is a study done by researchers at RAND. They reviewed policies on file with the insurance commissions in three states (CA, NY, and PA) between 2007 and 2017 to identify how carriers are assessing and pricing cyber risk. The researcher’s analysis revealed five pricing determinants.
1. Outside advice or loss data from industry, academic, and government reports;
2. Competitor’s pricing;
3. The experience and knowledge of the company’s underwriters;
4. Pricing from other insurance lines; and
5. Guesswork.
“From our analysis, the first and most important firm characteristic used to compute insurance premiums was the firm’s asset value (or revenue) base rate, rather than specific technology or governance controls.”
Wait…what?! Cyber insurers don’t care about cyber resilience or best practices?
To be fair, most policies analyzed in the RAND study required self-assessment questionnaires that asked for varying levels of detail related to a company’s security posture. However, questions were mostly focused on data type and volume and not on the security infrastructure.
To address the need for more sophisticated cyber risk assessments, insurers are increasingly turning to technology companies to provide analytics to develop coverage and pricing models. These companies are usually referred to as AppSec or InsurTech providers.
According to The World Insurance Report 2019, over 50% of insurers interviewed indicated partnerships with InsurTech firms or other risk analytics companies. By providing machine learning, aritificial intelligence-based products or advanced analytics, these companies enable underwriters to price risk on limited data.
What to Look For in a Cyber Policy
Before you start to evaluate cyber policies, be sure to select a broker and/or carrier that solely focuses on cyber insurance. Most companies look to buy insurance based on a budget rather than their actual risk exposure. A cyber-experienced broker can guide you to the appropriate coverage specific to your business.
So, what factors are important to consider when reviewing a cyber insurance policy?
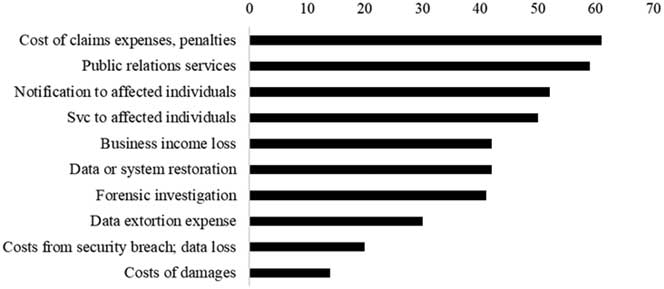
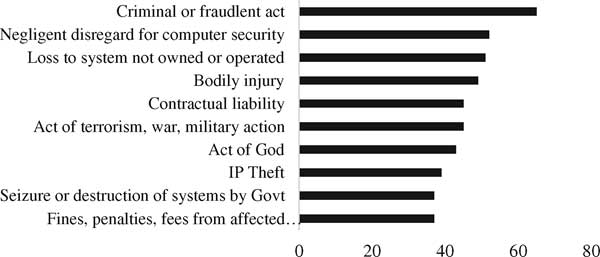
First, all policies list losses that are covered and those that are not. The RAND study compiled lists of the 10 most covered losses and the top 10 exclusions.
Most common covered losses
Most common exclusions
Next, don’t assume the common policy exclusions listed above are written in stone. Most exclusions can be negotiated.
· Be careful if you see a War and Terrorism Exclusion clause since 23% of cyber attacks are committed by nation states, according to Verizon.
· Look for indirect cost coverage, such as potential bankruptcy costs when a cyber attack compromises Intellectual Property.
· Investigate coverage for claims against you for breaches caused by you or your vendors on an outside network. As such, require cyber insurance for your vendors.
· Expect the policy to include Full Prior Acts coverage, which will cover any event that occurred in the past. This is vital considering many cyber events occur long before they are discovered.
· Be sure cybercrime events that utilize social engineering are covered. This includes Funds Transfer Fraud, Corporate Identity Theft and Phishing. According to the Willis Towers Watson 2017-2018 Reported Cyber Claims Index, the human element continues to be the leading cause of cyber loss, representing 61% of claims.
· Examine coverage for cyber-related property damage. Most cyber policies want to exclude it as a redundant coverage with General Liability policies. However, many General Liability policies exclude damage related to cyber event.
Take note of when coverage is triggered. For example, under the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA), which goes into effect in January 2020, privacy violations can occur in the absence of a breach. This wording is not likely in your policy.
Lastly, companies who can demonstrate a comprehensive cybersecurity plan with proven levels of security and internal controls receive better premium pricing. A cybersecurity services firm can prepare you by assessing your security infrastructure and making recommendations to lower your risk of a cyber event. They also can help with developing incident response plans and documenting security best practices.
The time to buy cyber insurance is now! Given the industry’s growth and profitablity, new carriers are entering the market and pressuring premium pricing. In fact, analysis of cyber incidents relative to their cyber premiums conducted by AIR indicates, “it’s likely that premiums being charged in the market are less than adequate to fully cover all sources of insured loss.”



