“It’s unwise to pay too much, but it’s worse to pay too little.” John Ruskin
Being frugal is admirable. Believe me, I hate waste and I can make a dollar talk. But there are some expenses, such as medical care, insurance, financial and legal advice…even paint, where pinching pennies ends up being more expensive. The same is true for eDiscovery.
Having said that, there are simple ways to bring down the cost of eDiscovery and it involves:
· Recognizing that a knowledge gap exists
· Thorough planning ahead of time
· Expert advice and guidance
THE KNOWLEDGE DISCONNECT
When it comes to eDiscovery, there is a knowledge gap for both clients and attorneys.
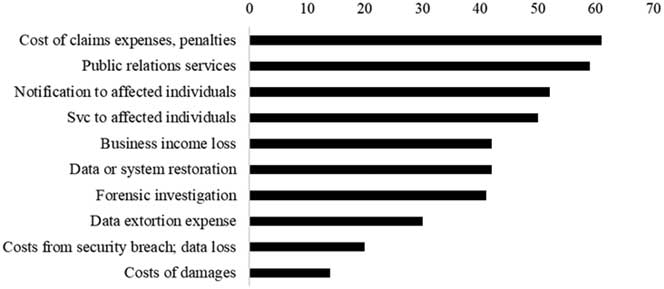
For clients, it’s hard to comprehend the unpredictable and opaque nature of eDiscovery costs and the wide fluctuation of these costs across individual cases. This is a justified frustration and a challenge that eDiscovery providers need to overcome.
For instance, a frequently-cited 2012 RAND study, identifies the average costs for eDiscovery production spanned a range of $17,000 to $27 million ($1.8 million median) for individual cases. That’s a meaningless estimate.
As for corporate eDiscovery, a 2018 survey by the Corporate Legal Operations Consortium (CLOC) found the average eDiscovery expense per year for companies was $2.8 million. (Mid-sized companies with annual revenue over $1B were 39.5% of respondents while large companies with $10B+ represented 46.5%).
Confusing cost structures is likewise an issue for litigators, but it’s the given process of eDiscovery that’s most burdensome. Attorneys need to have a level of knowledge about the available tools and technologies for a client’s specific eDiscovery needs, which is outside their area of expertise. For lawyers, it’s best to accept that your time is better spent on billable legal matters.
PLANNING AHEAD OF TIME IS KEY
Thoughtful planning with the goal of standardizing repeatable processes is the biggest initiative you can take toward reducing eDiscovery costs. While not everything can be standardized, think in terms of timelines and templates in keeping with best practices.
eDiscovery planning also includes collecting metrics to use as a reference for forecasting future costs and identifying any unnecessary outlays.
More than anything, planning eliminates the turmoil usually associated with eDiscovery. Getting started early and creating plans and protocols in advance is your best strategy for successfully navigating the process.
Create an ESI Protocol
Before a meet and confer, create a document with answers to frequently asked questions. Make sure you have extensive knowledge of your client’s data and the costs associated with the data you’re requesting from opposing.
Develop your ESI protocol so that it clearly addresses all necessary practices and procedures related to ESI in the case. This involves the technologies used, collection and culling methods, production specifications, and claw back provisions.
Cooperation between parties is essential because adversarial behavior makes eDiscovery very expensive. The earlier the terms of the ESI protocol are set and agreed upon, the lower the eDiscovery costs will be.
Proper Use of Legal Holds
According to Federal Rule of Civil Procedure Rule 26(b)(1), discovery in a civil case is available for “any nonprivileged matter that is relevant to any party’s claim or defense” and is proportional.
Therefore, when issuing a legal hold, it is helpful to have a process in place that lays out the specific data preservation expected and allows for negotiating cost-saving strategies such as phased discovery, sometimes referred to as data sweeps, and targeted data set collections.
Be specific about the data and documents that must be preserved and be sure to address automated IT functions so those operations can be stopped before data is unintentionally deleted, thereby hindering data acquisition.
Identify the Right People and Data Sources
Interviewing custodians is a quick way to identify the key people involved in the case, the relevant data, and where that data is located.
Ask custodians about devices, applications, and online accounts that might be tied to data sources, such as mobile and personal devices, and cloud-based storage. Recognize that archives, data backups or obsolete systems may contain important data and come into play when targeted data sources come up short or spoliation of the ESI has occurred.
This is also the time to inquire about data encryption, password controls and to request a data map of an organizations data and network structure.
Data Collection
Simply reducing the volume of data involved in eDiscovery is a surefire way to significantly lower costs. Use collection tools that filter data by time frame and file type. Cull data for responsive, non-privileged, and non-duplicative documents.
Phased discovery is another cost-saving approach that focuses on the most relevant data first and could decrease or eliminate the need for further discovery. It sweeps data sources to see what results are produced using targeted search terms and is a good means to triage data sources (are these the drones your looking for?)..
Keep in mind, mobile devices may not be the best source of data and may only produce more data to search through, so be selective when requesting devices.
Storage
Once data is collected, it must be stored in a secure repository, so consider the cost benefits of a shared repository.
Data Production
Production specifications ought to be addressed in the ESI Protocol. For added cost savings at this stage, explore rolling production, which starts with a limited production set (usually of the most critical data) and continues in stages.
The benefits of a rolling production include:
· Early identification of problems with production
· Timely agreement between parties that production matches the ESI protocol
· Access to critical data before all production is completed
Data Review
This is the costliest stage of the eDiscovery process with most estimates assigning 70-80% of discovery costs to document review.
The earlier stages of eDiscovery have focused on reducing the volume of data that gets to this stage. To realize additional cost savings, you need a clear and detailed review protocol in place, including a coding template.
Another option is Technology Assisted Review (TAR), which uses predictive coding to reduce costs. The caveat here is that TAR should only be done be someone with both legal and technical knowledge, or jointly with an expert in each discipline.
HIRING AN EXPERT IS GAME CHANGING
It’s expensive to bring an eDiscovery expert into your case and even more expensive if the case requires digital forensics. Nonetheless, it will likely be the difference between winning and losing. Better yet, you can share a neutral third-party expert with opposing counsel as a way to reduce this cost.
eDiscovery and digital forensics are complex fields that require years of training, including persistent continuing education to develop and maintain skills and techniques in the evolving technologies.
Experts have extensive knowledge of the variety of available forensic software applications and when to use them. Because they understand the types of data existing on different devices and can work across the wide range of operating system versions, they can provide invaluable advice during meet and confers and in preparing the ESI protocol.
Depending on the types of ESI being requested, an expert can advise the attorney on the proper data sources and devices to target. Moreover, an expert knows which types of data and approaches will be prudent in searching for answers and finding relevant ESI.
In fact, an eDiscovery expert can assist you in every stage of the eDiscovery process, which can bring down the overall discovery expense while you focus on the legal strategy.